Bot releases are visible (Hide)
REFACT
- Refactored to use a new pattern matching engine (SigFinder) for shellcode detection. Improved performance.
FEATURE
- Added new parameter
/pattern <file>allowing to supply custom signatures to be searched in memory. The format is defined by SigFinder and described in the relevant README. Ifpatternfile was defined, a .tag file for the found patterns will be generated, with the extension.pattern.tag - New fields in the
scan_report.json:- Save the PE-sieve version with which the scan was performed (
scanner_version) - In
workingset_scansection: addedpatternssection with information about found patterns:-
total_matched(count of all patterns matched, including the hardcoded ones) -
custom_matched(count of patterns matched from the set defined by the user inpatternfile)
-
- Save the PE-sieve version with which the scan was performed (
- New fields in the
dump_report.json:- If
pattern.tagfile was generated, the name of this file will be added in thepattern_tags_filefield of the relevant module.
- If
See also: HollowsHunter v0.3.9 & MalUnpack v0.9.9 with the latest PE-sieve
FEATURE
- New options for shellcode detection (
/shellc):- detect by patterns (previous mode): available with
/shellc P - detect by stats (new mode): available with
/shellc S - possibility to mix both modes: options
/shellc B(both) or/shellc A(any)
- detect by patterns (previous mode): available with
- Detection of obfuscated memory regions (
/obfusc) - Caching of detected shellcodes (guarantee that the dumped shellcode is the same as detected shellcode - no second read)
See also: HollowsHunter v0.3.8 & MalUnpack v0.9.8 with the latest PE-sieve
FEATURE
- improved integration with other languages (Python, Golang: https://github.com/hasherezade/pe-sieve/discussions/112), improvements in the API
- in ThreadScan: calculate the entropy of the detected area:
- decreased number of false positives (filtering by entropy)
- added a new section to the ThreadScanReport:
stats
- in dump report: set
"is_shellcode" : 1only if the code pattern was matched (to distinguish cases when i.e. the shellcode was encrypted and detected by thread scan)
BUGFIX
- fixed a bug in libPEconv (buffer boundary check: https://github.com/hasherezade/pe-sieve/commit/cabdd4691b37b81889fc29f437e990b8e6cf47a8)
- fixed crash if the output filter was set ( https://github.com/hasherezade/pe-sieve/discussions/113 - missing check if the dump report was generated )
- fixed backward compatibility with Windows XP ( #42 )
- decreased number of false positives when searching for PE files in non-executable memory
REFACT
- faster search for code signatures: skip padding from the scan
See also: HollowsHunter v0.3.6 & MalUnpack v0.9.7 with the latest PE-sieve
Published by hasherezade almost 2 years ago
FEATURE
- Added API function:
PESieve_scan_ex- allowing to retrieve scan and dump JSON reports directly into the supplied memory buffer ( Issue #105 ) - Allow to scan own workingset ( Issue #104 )
- Added one more shellcode pattern ( Issue #108 )
- Added version information to resources
BUGFIX
- Fixed getting stuck on scanning for PE artifacts (in some rare cases)
- Fixed checking mapped modules against the image on disk (fixed issue with the remote module not being copied)
- Fixed false positive - MUI files detected as implanted, when using 32bit scanner on 64bit system (FS redirection issue)
- Other small fixes
See also: HollowsHunter v0.3.5 & MalUnpack v0.9.6 with the latest PE-sieve

FEATURE
- In
/mignore- removed buffer limit (Details: https://github.com/hasherezade/pe-sieve/pull/99). WARNING: API change) - New param:
/threads, enabling scan of the threads' callstack . This is another layer of shellcode detection, allowing to capture "sleeping beacons", and others, decrypted just before the execution. (Read more here)

See also: HollowsHunter v0.3.4 with the latest PE-sieve
BUGFIX
- Fully redesigned IAT scan, providing much better precision (Issues: #98, #92, #77)
- Fixed processing PEs with relocation table containing empty records (https://github.com/hasherezade/libpeconv/issues/30)
- Fixed false positives in some of the code scans
FEATURE
- Added optional caching (Issue #94)
- Improved auto-detection of import reconstruction mode (
/imp A) : setR0,R1modes depending on the sizes of found IATs of particular types - Do not exclude .NET modules from code scan. Improved filtering of the changes typical for .NET.
- Changed reporting of IAT hooks to the format consistent with inline hooks reports ( more details here )
See also: HollowsHunter v0.3.3 & MalUnpack v0.9.1 with the latest PE-sieve

BUGFIX
- Fixed memory leak ( Issue #95 )
- Trim invalid sections while reconstructing the payload ( Issue #96 )
- Fixed overeager imports reconstruction ( Issue #97 )
- Improved auto-detection of import reconstruction mode
FEATURE
- Added new modes of import reconstruction (
/imp) :R0-R2: from restrictive to aggressive ( more info here ) - Report if the process reflection was used in a scan
- Automatically turn on
/reflmode if scan of inaccessible data requested (/data 4,/data 5)
See also HollowsHunter: https://github.com/hasherezade/hollows_hunter/releases/tag/v0.3.2

Published by hasherezade about 3 years ago
BUGFIX
- Fixed invalid condition check on scanning data (Issue #93)
- In imp rec auto mode (
/imp 1): do not overwrite import table of .NET modules (it was destroying imports) (Issue #89) - Improved detection if a PE is in a virtual or raw mode - fixed an issue in dumping of some PEs
- Improvements in code scan (Issue #15)
- Improved reporting of unreachable modules
See also HollowsHunter: https://github.com/hasherezade/hollows_hunter/releases/tag/v0.3.1.3
FEATURE
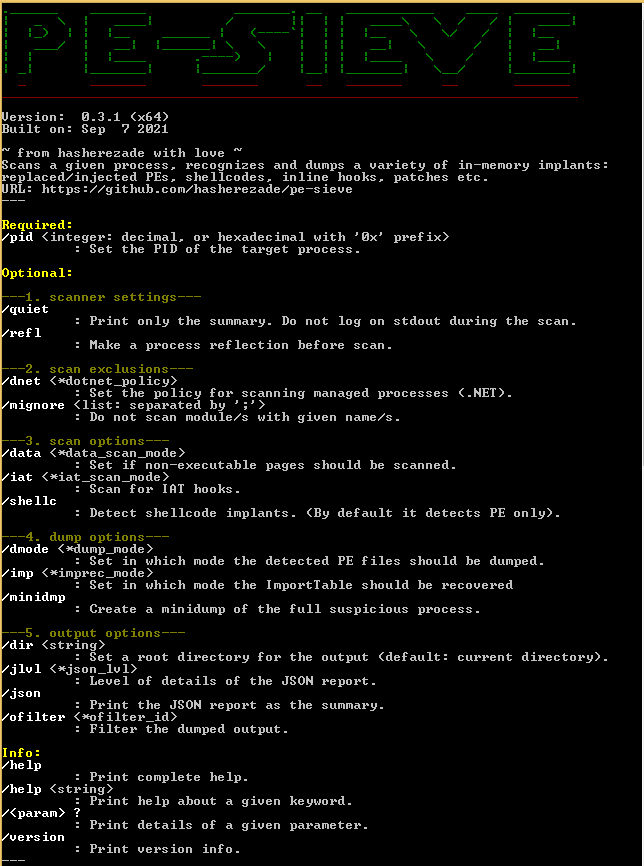
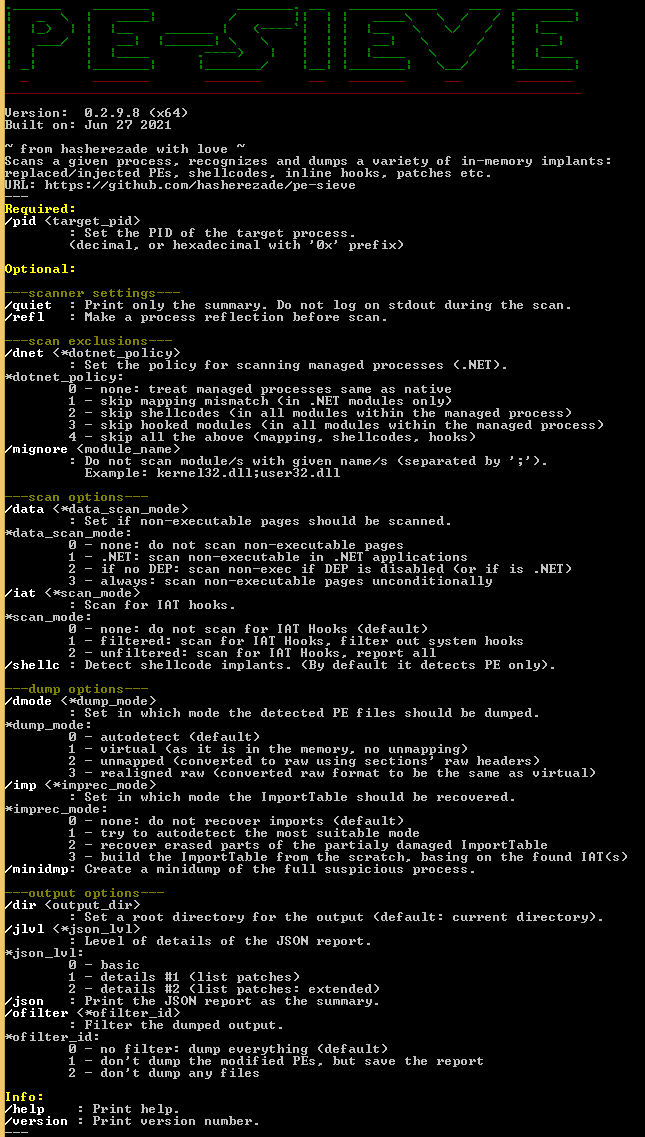
- Changes in presenting application parameters. Refactored to use ParamKit library
- Recognize Virtual Table hooks ( Issue #88 )
BUGFIX
- Improve recognizing when to rebuild import table from scratch ( Issue #89 )
- Improve detecting when to realign the payload ( Issue #90 )
- Do not include calls to own exports in the Import Table reconstruction ( Issue #91 )
See also HollowsHunter: https://github.com/hasherezade/hollows_hunter/releases/tag/v0.3.1
FEATURE
- supported force-read of inaccessible pages (
PAGE_NOACCESS) when running in the reflection mode (/refl):- automatic if the inaccessible page is within the PE module
- on-demand if the inaccessible page is somewhere else in the workingset (depending on the selected
/datamode)
- added more options for scanning non-executable pages (
/data) - added one more mode of IAT hooks scan (
/iat), allowing to filter out hooks that lead to any system DLL - in hook resolving function: recognize and parse one more jump type
- in shellcode detection: added one more pattern
BUGFIX
- Fixed error in printing JSON reports of some of the scan types (missing headers)
REFACT
- refactoring and optimization of the function resolving hooks
- removed not needed flags for process reflection creation (optimization)
See also HollowsHunter: https://github.com/hasherezade/hollows_hunter/releases/tag/v0.3.0
FEATURE
- added a new pattern for detecting 64-bit shellcodes
- added return codes informing about the result of the run
- removed unused parameter :
/mfilter - in JSON: added an indicator if the replaced module was linked to the PEB
BUGFIX
- Fixed error in dumping some of the PEs (issue caused by the invalid ImageSize calculated: Issue #85)
FEATURE
- Improved parameters accessibility: grouped into more categories, sorted.
- Display hints for misspelled parameters
- Added parameter
jlvlallowing to regulate the level of details included in the JSON report. Allow to list hooks/patches in thescan_report. - Improved hook parsing: identify hooks created by replacing the target of existing JMP/CALL
BUGFIX
- Improved reading remote memory (fixed a bug that was causing PE-sieve to stuck in some cases of reading inaccessible memory)
- Do not include initial protection in the check of memory access rights
FEATURE
- In DLL: use
__cdeclcalling convention (instead of__stdcall) - In case if scanning data is enabled (
/dataparameter) scan for hooks also the sections that are marked as non-executable (if they contain code patterns) - Added a count of sections scanned for patches to the report
BUGFIX
- Fixed a bug in detecting a section with Entry Point (affecting unpacking of some packers, such as ASPack - Issue #73 )
- Fixed bug in libPEconv: do not treat empty relocation blocks as invalid
REFACT
- Some internal cleanup and refactoring
Published by hasherezade about 4 years ago
BUGFIX:
- Fixed error in scanning workingset of some applications (Issue #68)
Published by hasherezade about 4 years ago
BUGFIX
- Fixed broken detection of ASProtect ( Issue #66 )
- Fixed broken parsing of a hexadecimal PID ( Issue #65 )
- Fixed errors on code scan (caused by invalid relocation table check)
- Do not assume that the section 0 is always executable
- Fixed bug in scanning 64bit modules by a 32bit scanner
FEATURE
- Added one more pattern to detect 64 bit code
REFACT
- Refactored identifying executable sections
Published by hasherezade over 4 years ago
BUGFIX
- Fixed hanging during the IAT scan of some PEs
- Fixed error in converting paths from the
/Device/format - Fixed not listing results of the mapping scan in the summary
FEATURE
- added one more .NET policy (in
/dnetparameter) - In the summary: changed
detachedtounreachable_file
Published by hasherezade over 4 years ago
FEATURE
- Detailed info about a single parameter can be requested by:
/<parameter> ? - New modes in the
/dataparameter - New parameter
/dnetallowing to enable treating .NET modules differently than native ones - Report about PE implants and shellcode implants separately
- Added information in the report: process bitness, is process managed (vs native)
- Minor changes in the API:
PEsieve_versionimplemented as a constant - Allow for partial scanning of 64 bit processes by a 32 bit scanner
BUGFIX
- If the parameter
/reflchosen, the process reflection should be used for both scan and dump - Fixed switching back to the original console color after printing in color (improved look on Powershell console)
- Fixed recognizing if the PE in the memory is in raw or virtual mode (it was giving invalid results for some payloads)
- Fixed broken parameter
/mfilter
REFACT
- Refactored parsing of the parameters
- Internal refactoring and cleanup of the scanner
FEATURE
- New parameter:
/reflallowing to make a process reflection before scanning - Support scanning PEs with no sections (i.e. packed with Crinkler) (Issue #46)
- Allow to build as static library
- Dump report about hooks even if dumping the modules failed
- Show the time of scanning workingset
BUGFIX
- Fixed JSON in code scan report (in case of reporting errors)
- Fixed problems with dumping PEs with bogus Image Size (prevent crashes, try to autodetect the correct size)
REFACT
- Internal refactoring (i.e. in scanning workingset)
- Set debug privilege unconditionally










