gitleaks
Protect and discover secrets using Gitleaks 🔑
MIT License
Bot releases are hidden (Show)
Changelog
- 02808f4 Limit hashicorp-tf-password to .tf/.hcl files (#1420)
- 07e1c30 rm print
- db63fc1 reduce telegram... todo url and xml for later
- 9a4538c coderabbit.ai <3
- fe94ef9 Add NewRelic insert key detection (#1417)
- bb4424d Improved Telegram bot token rule regex and added more test cases (#1404)
- 575e923 Add intra42 client secret (#1408)
Shout out to @coderabbit for their sponsorship!
Published by zricethezav 5 months ago
Changelog
- 39947b0 extend FB access token discovery (#1407)
- 79cac73 tests: scalingo validation consistent test (#1359)
- 247f423 add real (test) standard and restricted keys (#1375)
- 821b232 Add Cloudflare API and Origin CA keys (#1374)
- 57ac4b3 Update "contributing guidelines" link (#1390)
- db69e82 add update token from square (#1370)
- 4b54328 feat: facebook secret, access token, and page access token rules (#1372)
- 979f213 update mailchimp with new tokens (#1376)
- 59c0cc7 Append ordered rules when extending (#1304)
- 6c52f87 fix: age rule id with dashes (#1349)
- 247a5e7 patching golang.org/x/text for CVE-2021-38561 and CVE-2022-32149 (#1342)
- 8d23afd Use latest base images. (#1334)
Published by zricethezav 9 months ago
Changelog
- ac4b514 removed gitleaks user from Dockerfile (#1313)
- 76c9e31 Remove IAM identifiers for non-credential resources in the aws-access-token rule (#1307)
- afe046b Update stripe rule to not alert on publishable keys (#1320)
- 8b8920d --max-target-megabytes flag now supported for --no-git flag as well (#1330)
- a59289c add pre-commit hook gitleaks-system (#1225)
- 870194b fix errors when using protect and an external git diff tool (#1318)
- 179c607 rename filesystem to directory (#1317)
- 8de8938 Enhance Secret Descriptions (#1300)
- ca7aa14 Small refactor
detectandsources(#1297) - 01e60c8 chore(config): refactor to go generate; simplify configRules init (#1295)
- 54f5f04 forgot symlinks
- 221d5c4 pretty apparent 'protect' and 'detect' should be merged into one command (#1294)
- 128b50f style: sort the stopwords (#1289)
Published by zricethezav 11 months ago
Changelog
- dab7d02 dont crash on 100gb files pls (#1292)
- e63b657 remove secretgroup from default config (#1288)
- 20fcf50 feat: Hashicorp Terraform fields for password (#1237)
- b496677 perf: avoid allocations with
(*regexp.Regexp).MatchString(#1283) - a3ab4e8 refactor: more explicit rules (#1280)
- bd9a25a bugfix: reduce false positives for stripe tokens by using word boundaries in regex (#1278)
- 6d0d8b5 add Infracost API rule (#1273)
- 2959fc0 refactor: simplify test asserts (#1271)
- d37b38f Update Makefile
- 14b1ca9 refactor: change detect tests to t.Fatal instead of log.Fatal (#1270)
- d9f86d6 feat(rules): Add detection for Scalingo API Token (#1262)
- ed34259 feat(jwt): detect base64-encoded tokens (#1256)
- 0d5e46f feat: add --ignore-gitleaks-allow cmd flag (#1260)
- a82ac29 switch out libs (#1259)
- 0b84afa fix: no-color option should also affect zerolog output (#1242)
- 8976539 Fixed lineEnd indexing if the match is the whole line (#1223)
- 30c6117 feat: Add optional redaction value, default 100 (#1229)
- e9135cf fix(jwt): longer segment lengths (#1214)
- f65f915 Added yarn.lock file to default allowlist paths (#1258)
- abfd0f3 Update README.md
- 18283bb feat(rules): make case insensitivity optional (#1215)
- 9fb36b2 feat(rules): detect Hugging Face access tokens (#1204)
- db4bc0f Resolve #1170 - Enable selection of a single rule (#1183)
- 3cbcda2 Update authress.go to include alternate form account dash (-) (#1224)
- 46c6272 refactor: remove unnecessary removing temp files in tests (#1255)
- 963a697 refactor: use os.ReadFile instead of os.Open + io.ReadAll (#1254)
- 163ec21 fix(sumologic): improve patterns (#1218)
Published by zricethezav about 1 year ago
What's Changed
- Fix inconsistent generated values in config by @rgmz in https://github.com/gitleaks/gitleaks/pull/1200
- feat: add JFrog API and Identity keys by @baruchiro in https://github.com/gitleaks/gitleaks/pull/1233
- Add entropy check to plaid client/secret ID rules by @mortenson in https://github.com/gitleaks/gitleaks/pull/1213
- Update config template logic by @rgmz in https://github.com/gitleaks/gitleaks/pull/1201
- Include entropy in Plaid rule file by @rgmz in https://github.com/gitleaks/gitleaks/pull/1252
- refactor: fix #722 properly by @L11R in https://github.com/gitleaks/gitleaks/pull/1250
New Contributors
- @baruchiro made their first contribution in https://github.com/gitleaks/gitleaks/pull/1233
- @mortenson made their first contribution in https://github.com/gitleaks/gitleaks/pull/1213
- @L11R made their first contribution in https://github.com/gitleaks/gitleaks/pull/1250
Full Changelog: https://github.com/gitleaks/gitleaks/compare/v8.17.0...v8.18.0
Published by zricethezav over 1 year ago
What's Changed
- Add
REDACTEDto stopwords forgeneric-api-keyrule by @9999years in https://github.com/gitleaks/gitleaks/pull/1188 - Add detection for Snyk tokens by @wayne-snyk in https://github.com/gitleaks/gitleaks/pull/1190
- Add makefile variable detections by @wayne-snyk in https://github.com/gitleaks/gitleaks/pull/1191
- chore: update deps to fix solaris #1158 by @gaige in https://github.com/gitleaks/gitleaks/pull/1159
- Add junit report format by @maltemorgenstern in https://github.com/gitleaks/gitleaks/pull/920
- Ignore all comits when
.gitleaksignorefingerprint lacks SHA by @rgmz in https://github.com/gitleaks/gitleaks/pull/1156 - Improved global exclusion list by @sergiomarotco in https://github.com/gitleaks/gitleaks/pull/1193
- Add detection for OpenAI API keys by @Becojo in https://github.com/gitleaks/gitleaks/pull/1148
- Add warning for quoted
--log-optsvalues by @rgmz in https://github.com/gitleaks/gitleaks/pull/1160 - Fixed docker run command in README.md by @IanMoroney in https://github.com/gitleaks/gitleaks/pull/1194
- add tags support for csv and sarif formats by @eyalatox in https://github.com/gitleaks/gitleaks/pull/1176
- Update Slack token regexes by @rgmz in https://github.com/gitleaks/gitleaks/pull/1161
New Contributors
- @9999years made their first contribution in https://github.com/gitleaks/gitleaks/pull/1188
- @wayne-snyk made their first contribution in https://github.com/gitleaks/gitleaks/pull/1190
- @gaige made their first contribution in https://github.com/gitleaks/gitleaks/pull/1159
- @IanMoroney made their first contribution in https://github.com/gitleaks/gitleaks/pull/1194
- @eyalatox made their first contribution in https://github.com/gitleaks/gitleaks/pull/1176
- @dvasdekis made their first contribution in https://github.com/gitleaks/gitleaks/pull/1079
Full Changelog: https://github.com/gitleaks/gitleaks/compare/v8.16.4...v8.17.0
Published by zricethezav over 1 year ago
Changelog
- 6f75511 Added option to specify .gitleaksignore path (#1179) @pacorreia
- 190ac97 Fix closing file in writeJson and writeSarif (#1187) @alexandear
- 6dbb0c5 Simplify tests by using T.TempDir (#1186) @alexandear
- 6705461 Fix typos in *.md, comments and logs (#1185) @alexandear
- 9869eab Update README.md
- 16f1ec0 Update bug_report.md
- 8d80a5a Adding discord channel to readme
- 146f69e 🐛 fix(sarif): update report to pass validator (#1167) @DariuszPorowski
Published by zricethezav over 1 year ago
Changelog
- 51ca0f8 fix(detect): extra secret from group before checking allowlist (#1152)
- 81cf308 Fix G307 warning: Deferring unsafe method "Close" on type "*os.File" (#1154)
- bd8b145 fix(detect): avoid panic with verbose flag (#1143)
- 839f114 Fix typo (#1142)
- 63c3076 No color (#1136)
- 56079dc safer out of bounds (#1135)
- 9c6650d Add Authress access key format: https://authress.io/knowledge-base/docs/authorization/service-clients/secrets-scanning/ (#1131)
- 6fa63f4 Update pre-commit address and rev tag in README (#1125)
- 9701bf1 Bufix/1100 protect stagged files (#1121)
- db79d81 fix README.md !? (#1123)
- 8a31f4a Improve rule descriptions for Stripe and Facebook access tokens (#1119)
- 6b0c303 Add Defined Networking API Tokens (#1096)
Huuuuuge thank you to all the contributors especially @rgmz
@edwardwang888 @wparad @sadikkuzu @RafaelFigueiredo @fgreinacher @jasikpark @sergiomarotco
Published by zricethezav over 1 year ago
Changelog
- 63c3076 No color (#1136)
- 56079dc safer out of bounds (#1135) (Thank you @agmond)
- 9c6650d Add Authress access key format: https://authress.io/knowledge-base/docs/authorization/service-clients/secrets-scanning/ (#1131)
- 6fa63f4 Update pre-commit address and rev tag in README (#1125)
- 9701bf1 Bufix/1100 protect stagged files (#1121)
- a5b9c24 remove extra default on source option
- db79d81 fix README.md !? (#1123)
- 8a31f4a Improve rule descriptions for Stripe and Facebook access tokens (#1119)
- 6b0c303 Add Defined Networking API Tokens (#1096)
Thanks to @americanair for sponsoring this open source project!
Thanks to all the contributors this release: @fgreinacher @wparad @RafaelFigueiredo @sergiomarotco @jasikpark
Published by zricethezav over 1 year ago
Changelog
- 1fb3a77 Update gitleaks.toml (#1116)
- 11c2ad0 Add gradle.lockfile to allowlist (#1112)
- e55d397 Update pre-commit rev tag in README (#1108)
- 2dd9946 Add pnpm-lock.yaml and Database.refactorlo (#1109)
Published by zricethezav over 1 year ago
Changelog
- 4b5e8e1 Feat/allowlist regex target (#1107)
Allowlist Regex Targets
Let's use the generic rule to demonstrate the new regexTarget allowlist option
[[rules]]
description = "Generic API Key"
id = "generic-api-key"
regex = '''(?i)(?:key|api|token|secret|client|passwd|password|auth|access)(?:[0-9a-z\-_\t .]{0,20})(?:[\s|']|[\s|"]){0,3}(?:=|>|:=|\|\|:|<=|=>|:)(?:'|\"|\s|=|\x60){0,5}([0-9a-z\-_.=]{10,150})(?:['|\"|\n|\r|\s|\x60|;]|$)'''
secretGroup = 1
entropy = 3.5
keywords = [
"key","api","token","secret","client","passwd","password","auth","access",
]
example.txt will be our target and contain a single line with a fake secret:
var discord_client_secret = '8dyfuiRyq=vVc3RRr_edRk-fK__JItpZ'
Running gitleaks on this file using the generic rule will return one finding:
gitleaks detect --source=example.txt --no-git -v --config=example.toml
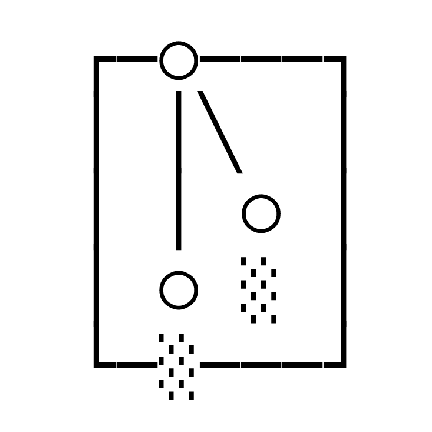
○
│╲
│ ○
○ ░
░ gitleaks
Finding: discord_client_secret = '8dyfuiRyq=vVc3RRr_edRk-fK__JItpZ'
Secret: 8dyfuiRyq=vVc3RRr_edRk-fK__JItpZ
RuleID: generic-api-key
Entropy: 4.413910
File: example.txt
Line: 1
Fingerprint: example.txt:generic-api-key:1
We can add a allowlist regexes entry to include part of the secret. This will cause gitleaks to ignore the finding above.
Note that by default gitleaks uses the Secret to compare against allowlist regexes.
Adding the following allowlist to the generic rule will cause gitleaks to ignore the finding:
[rules.allowlist]
regexes = ["vV"]
But now say you don't want to use Secret to compare against your allowlist regexes. Well, now you can use regexTarget and set the value as either line or match to compare against the line or regex match:
[rules.allowlist]
regexTarget = "match"
regexes = ["discord"]
and
[rules.allowlist]
regexTarget = "line"
regexes = ["var"]
will both result in the finding being ignored because discord is found in the generic rule regex match and var is in the line where the finding was found.
In addition to rule allowlists, you can set regexTarget in the global allowlist:
[allowlist]
regexTarget = "line"
regexes = ["var"]
Thanks @bplaxco for the review
Published by zricethezav over 1 year ago
Changelog
- 343e693 ignore package-lock.json (#1076)
- 0060ab6 Fix typos in README.md and CONTRIBUTING.md (#1090)
- 0259088 fix: ignore baseline if path was not relative in source (#1101)
- 088f8b8 Fix H in GitHub and update pre-commit rev tag in README (#1087)
Shouts outs to @sandyydk @raffis @lawndoc @sadikkuzu
Published by zricethezav over 1 year ago
Changelog
- afdccad Add missing GitLab token patterns (#1077)
- e002920 Fix rule for private keys (#1072)
Published by zricethezav almost 2 years ago
Changelog
- d805fb9 remove color formatting when #1042 is encountered (#1050)
- 391d4d7 Update README.md
- f774932 adding jwt tokens with padding format "=" (#1031)
Published by zricethezav almost 2 years ago
bumping deps
Published by zricethezav almost 2 years ago
Actually publish this test
Published by zricethezav almost 2 years ago
This release is a pre-release test for adding additional labels to the docker image
Published by zricethezav almost 2 years ago
Changelog
- 7f229fa include default newline pairs when calculating location (#1038)
- d0733f9 Add rule for fine-grained GitHub PAT (#1026)
Published by zricethezav about 2 years ago
Changelog
- 6ef704f Add scanning from a pipe with --pipe (#1012)
- 6d801ed Add support for following symlinks (#1010)
- e15ab0d fix bug in readme (#1011)
Thanks @RickyGrassmuck @sergiomarotco
--pipe
Try --pipe with anything...
git log -p | gitleaks detect --pipe
--follow-symlinks
gitleaks --source . --no-git --follow-symlinks
Published by zricethezav about 2 years ago
Changelog
- c39e764 define log-opts, odd that this wasn't failing before... (#1009)
